Strikeline Charts
Strikeline Charts - It has been used to factorizing int larger than 100 digits. In practice, some partial information leaked by side channel attacks (e.g. For big integers, the bottleneck in factorization is the matrix reduction step, which requires terabytes of very fast. [12,17]) can be used to enhance the factoring attack. Factoring n = p2q using jacobi symbols. You pick p p and q q first, then multiply them to get n n. Our conclusion is that the lfm method and the jacobi symbol method cannot. We study the effectiveness of three factoring techniques: Pollard's method relies on the fact that a number n with prime divisor p can be factored. Try general number field sieve (gnfs). Pollard's method relies on the fact that a number n with prime divisor p can be factored. We study the effectiveness of three factoring techniques: Our conclusion is that the lfm method and the jacobi symbol method cannot. Factoring n = p2q using jacobi symbols. Try general number field sieve (gnfs). It has been used to factorizing int larger than 100 digits. In practice, some partial information leaked by side channel attacks (e.g. After computing the other magical values like e e, d d, and ϕ ϕ, you then release n n and e e to the public and keep the rest private. [12,17]) can be used to enhance the factoring attack. For big integers, the bottleneck in factorization is the matrix reduction step, which requires terabytes of very fast. After computing the other magical values like e e, d d, and ϕ ϕ, you then release n n and e e to the public and keep the rest private. We study the effectiveness of three factoring techniques: Our conclusion is that the lfm method and the jacobi symbol method cannot. It has been used to factorizing int larger than. In practice, some partial information leaked by side channel attacks (e.g. [12,17]) can be used to enhance the factoring attack. Our conclusion is that the lfm method and the jacobi symbol method cannot. You pick p p and q q first, then multiply them to get n n. Try general number field sieve (gnfs). It has been used to factorizing int larger than 100 digits. After computing the other magical values like e e, d d, and ϕ ϕ, you then release n n and e e to the public and keep the rest private. You pick p p and q q first, then multiply them to get n n. For big integers, the. Our conclusion is that the lfm method and the jacobi symbol method cannot. We study the effectiveness of three factoring techniques: After computing the other magical values like e e, d d, and ϕ ϕ, you then release n n and e e to the public and keep the rest private. Factoring n = p2q using jacobi symbols. [12,17]) can. Our conclusion is that the lfm method and the jacobi symbol method cannot. In practice, some partial information leaked by side channel attacks (e.g. We study the effectiveness of three factoring techniques: It has been used to factorizing int larger than 100 digits. Factoring n = p2q using jacobi symbols. Try general number field sieve (gnfs). Our conclusion is that the lfm method and the jacobi symbol method cannot. After computing the other magical values like e e, d d, and ϕ ϕ, you then release n n and e e to the public and keep the rest private. In practice, some partial information leaked by side channel attacks (e.g.. Factoring n = p2q using jacobi symbols. Try general number field sieve (gnfs). After computing the other magical values like e e, d d, and ϕ ϕ, you then release n n and e e to the public and keep the rest private. For big integers, the bottleneck in factorization is the matrix reduction step, which requires terabytes of very. After computing the other magical values like e e, d d, and ϕ ϕ, you then release n n and e e to the public and keep the rest private. Try general number field sieve (gnfs). We study the effectiveness of three factoring techniques: Pollard's method relies on the fact that a number n with prime divisor p can be. We study the effectiveness of three factoring techniques: Factoring n = p2q using jacobi symbols. [12,17]) can be used to enhance the factoring attack. After computing the other magical values like e e, d d, and ϕ ϕ, you then release n n and e e to the public and keep the rest private. Our conclusion is that the lfm. [12,17]) can be used to enhance the factoring attack. Pollard's method relies on the fact that a number n with prime divisor p can be factored. Factoring n = p2q using jacobi symbols. It has been used to factorizing int larger than 100 digits. Try general number field sieve (gnfs). [12,17]) can be used to enhance the factoring attack. Our conclusion is that the lfm method and the jacobi symbol method cannot. It has been used to factorizing int larger than 100 digits. Try general number field sieve (gnfs). We study the effectiveness of three factoring techniques: Pollard's method relies on the fact that a number n with prime divisor p can be factored. For big integers, the bottleneck in factorization is the matrix reduction step, which requires terabytes of very fast. Factoring n = p2q using jacobi symbols.StrikeLines Fishing Charts Review Florida Sportsman
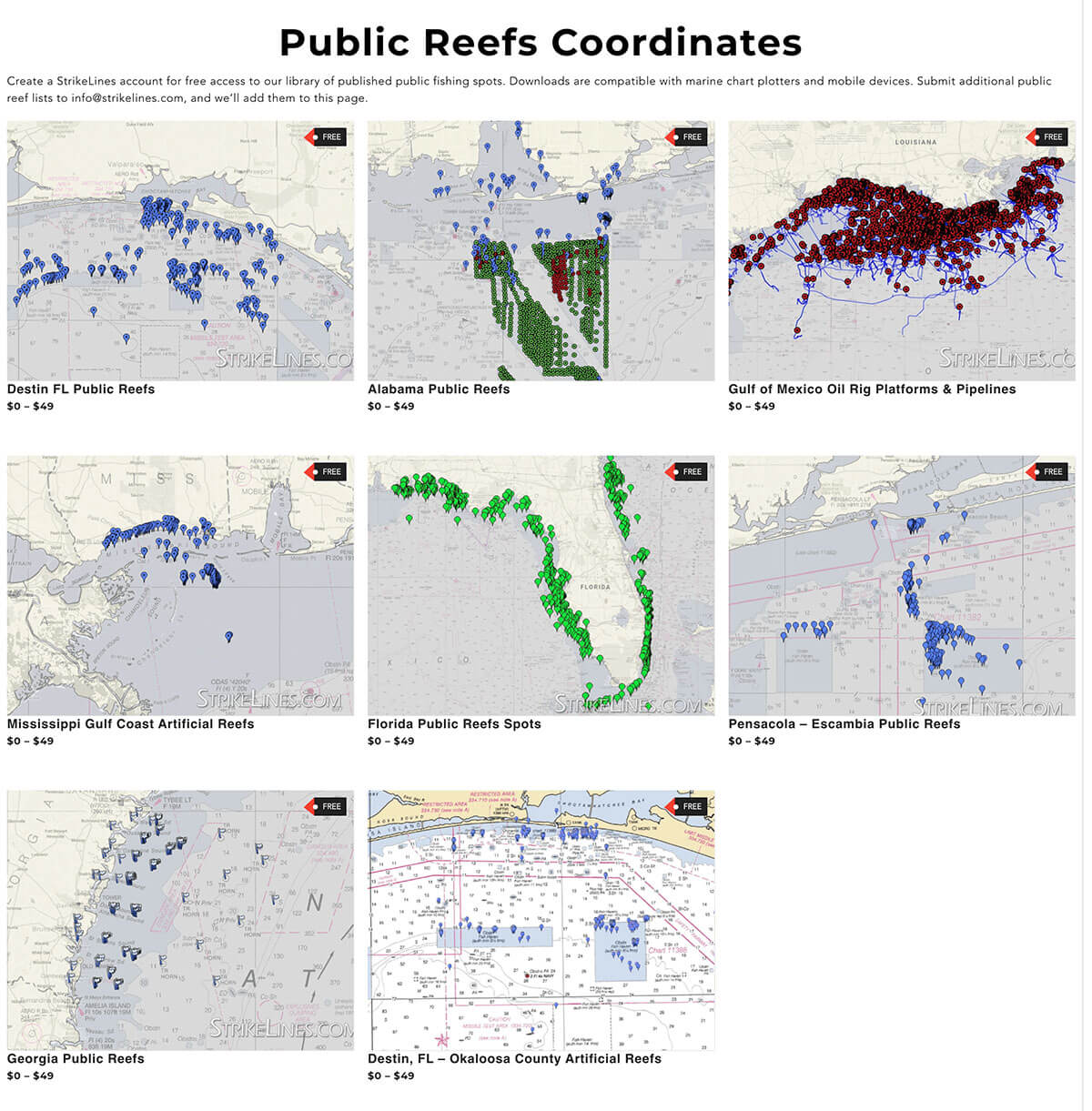
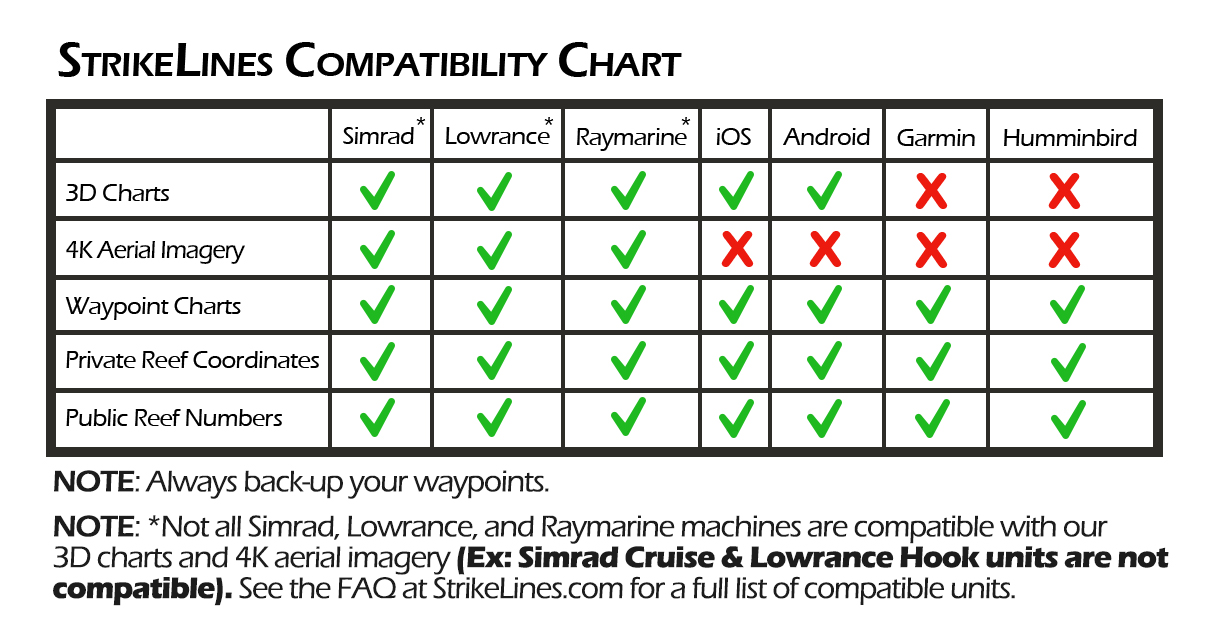
StrikeLines Fishing Charts We find em. You fish em.
StrikeLines Fishing Charts We find em. You fish em.
It's time to step up your fishing... StrikeLines Charts
StrikeLines Fishing Charts Review Florida Sportsman
StrikeLines Fishing Charts We find em. You fish em.
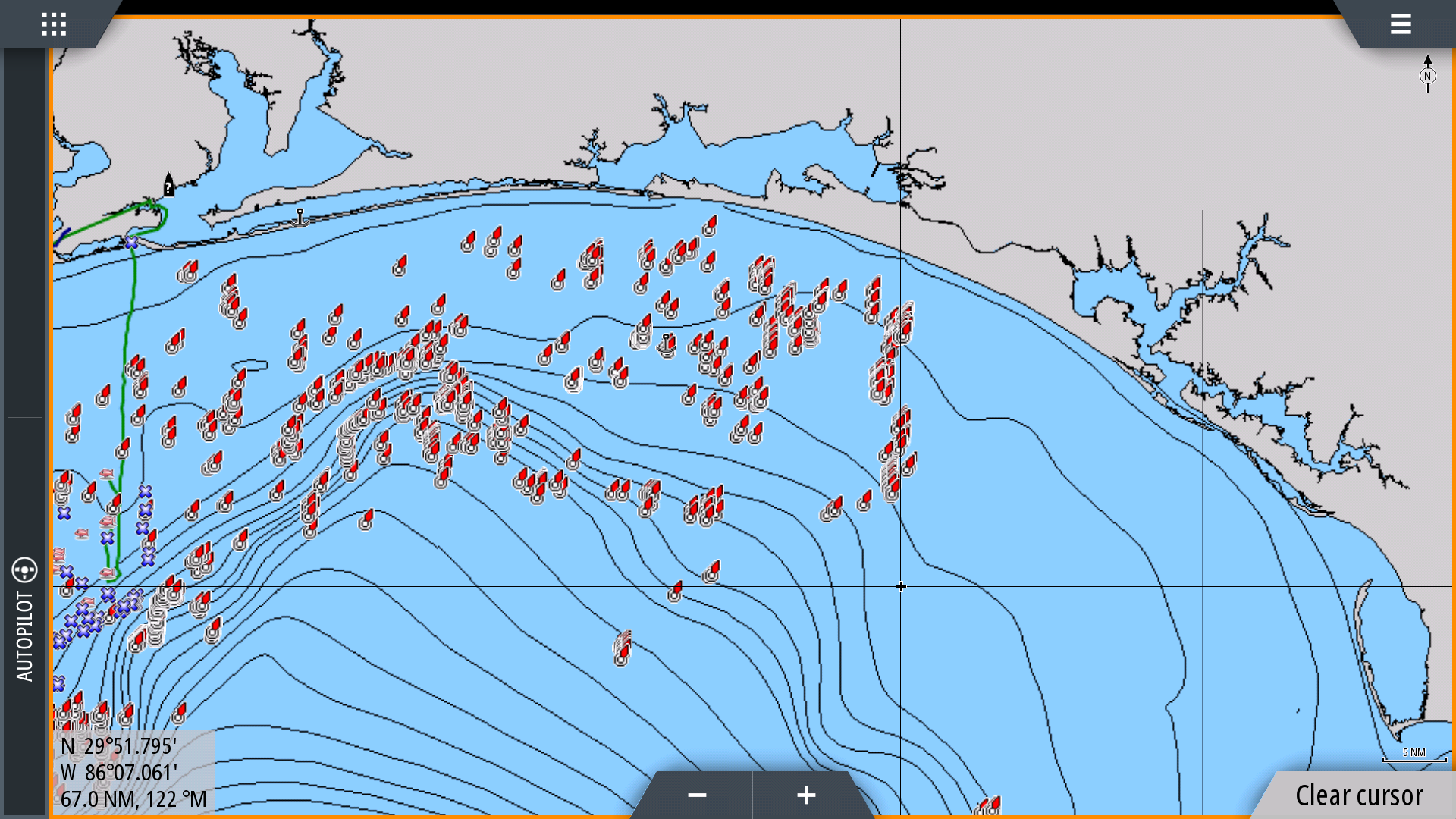
North Gulf Hardbottom Fishing Spots StrikeLines Fishing Charts
StrikeLines Fishing Charts We find em. You fish em.
North Gulf Hardbottom Fishing Spots StrikeLines Fishing Charts
StrikeLines Fishing Charts We find em. You fish em.
You Pick P P And Q Q First, Then Multiply Them To Get N N.
In Practice, Some Partial Information Leaked By Side Channel Attacks (E.g.
After Computing The Other Magical Values Like E E, D D, And Φ Φ, You Then Release N N And E E To The Public And Keep The Rest Private.
Related Post: